Protecting your business from cyberattacks is our #1 priority
Trust MicroSecure, a division of Team Microfix, an ISO 27001:2022 certified company that, in partnership with Fortinet, offers a SOC service suitable for small and medium businesses.
![csoc-bg[1]](https://www.microsecure.com/wp-content/uploads/2021/12/csoc-bg1.png)
Cybersecurity: a vast perimeter to defend while playing on multiple chessboards.
Advanced analysis
24x7 alerts
AI analysis
Incident management
Intervention
Vulnerability report
A report and a session with a cybersecurity expert to discuss identified events and recommendations.
Latest generation EDR antivirus, a proven and acclaimed solution to protect your business
Protect your business with the next-generation EDR (Endpoint Detection and Response) antivirus. Traditional antiviruses that work by signature detection are no longer able to effectively counter the most recent attacks. In addition to traditional antiviral signatures, EDRs analyze behavior using artificial intelligence (AI) algorithms. A “zero day” attack (still unknown to date) will therefore be detected by the EDR software which, being very reactive, will react to the unusual behavior of this new virus.

Vulnerability scan
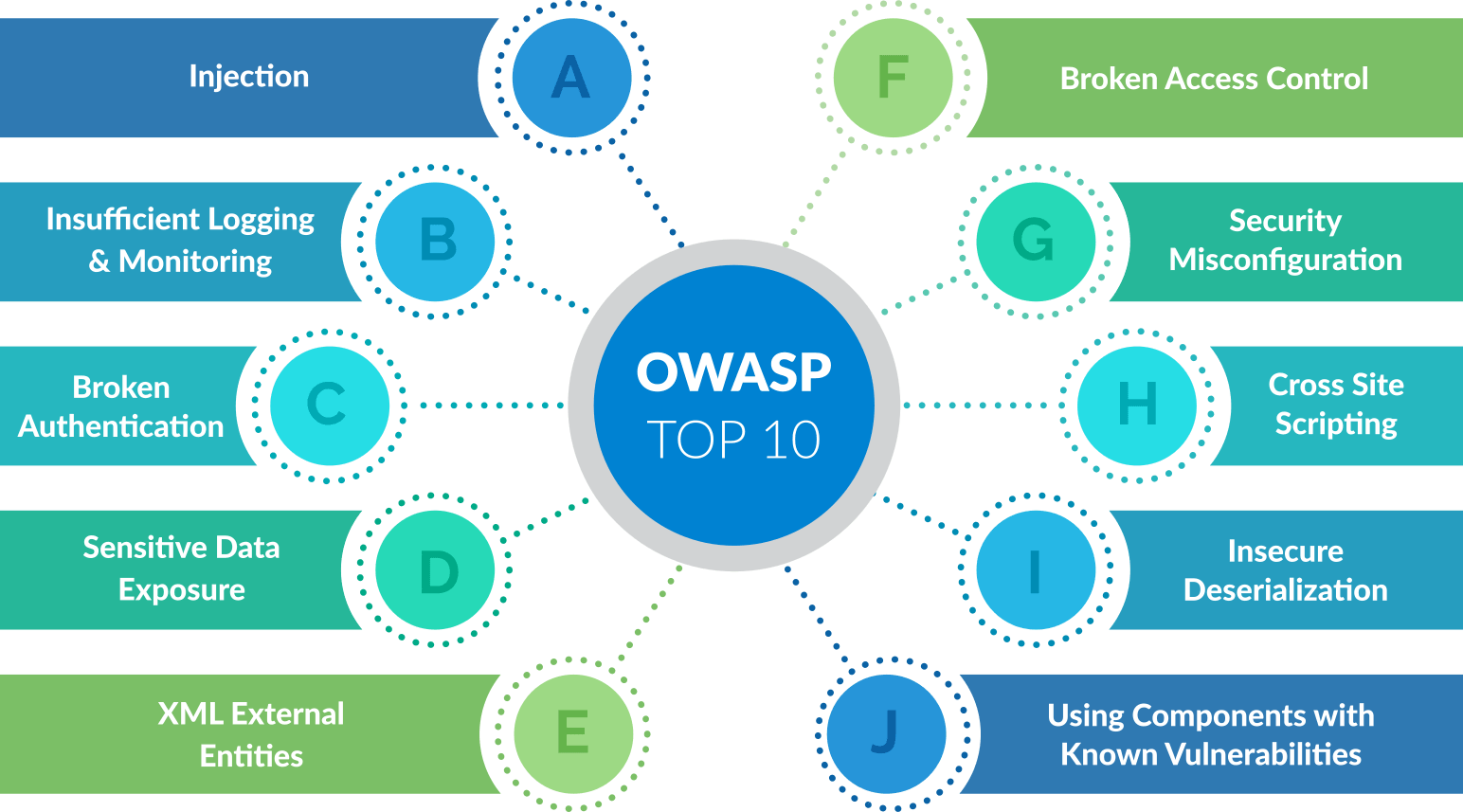
To validate your web applications, we perform a variety of tests based on the Open Web Application Security Project (OWASP) which will clearly identify risks and vulnerabilities.
Cybersecurity review
Assessing your cybersecurity posture helps identify weaknesses and vulnerabilities to fully understand the risks associated with your current situation. Our recommendation report will help you make the right decisions and invest in the right places in order of priority.

![banner1_dn_en[1]](https://www.microsecure.com/wp-content/uploads/2021/12/banner1_dn_en1.jpg)
Dark Web monitoring
A dark web monitoring service in order to let you know when your passwords are on sale or publicly available. Contrary to popular belief, it is often in simplicity that hackers find their access.
Don’t wait for a cyberattack to target you!
Hackers won’t wait, contact us to protect you before it’s too late.
